
y2k Clutch Bag Red - Gem

Buy Preloved Clutch Bags from Second Edit by Style Theory – Page 2

The Koa Bag, Style Inspiration, Summer 2022

y2k Clutch Bag Red - Gem
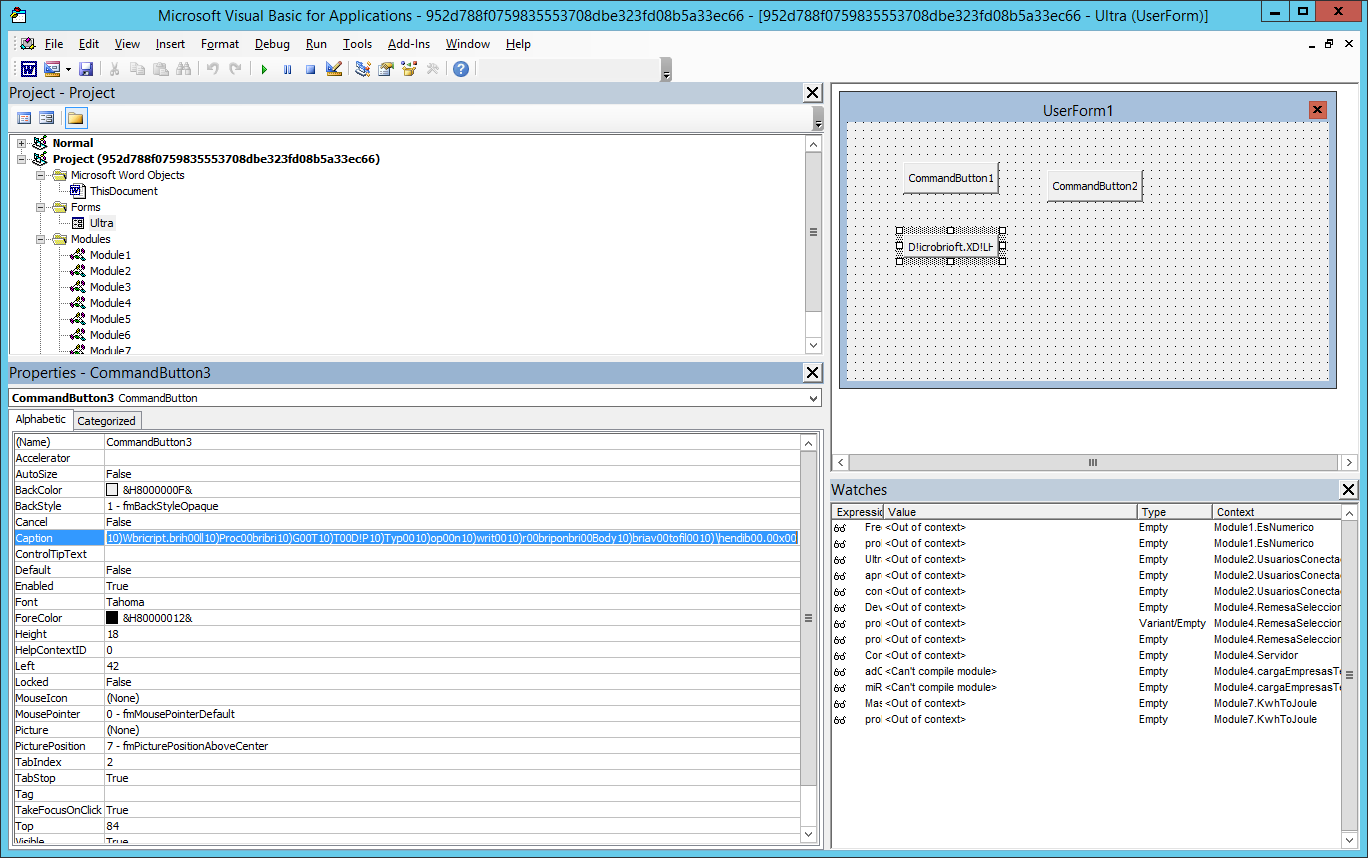
Microsoft Warns of Sneaky New Macro Trick - vulnerability database

Buy Clutch Bags from Second Edit by Style Theory – Page 2

1920s Clutch Bags for sale
coding-challenge/events.json at master · hangtime/coding-challenge

argilla/comparison-data-falcon-with-feedback · Datasets at Hugging
Multiple Cobalt Personality Disorder - vulnerability database

AMD Response to Log4j (Log4Shell) Vulnerability - vulnerability
