Do NOT report security vulnerabilities, report impacts instead!, by Ricardo Iramar dos Santos
Vulnerability Report
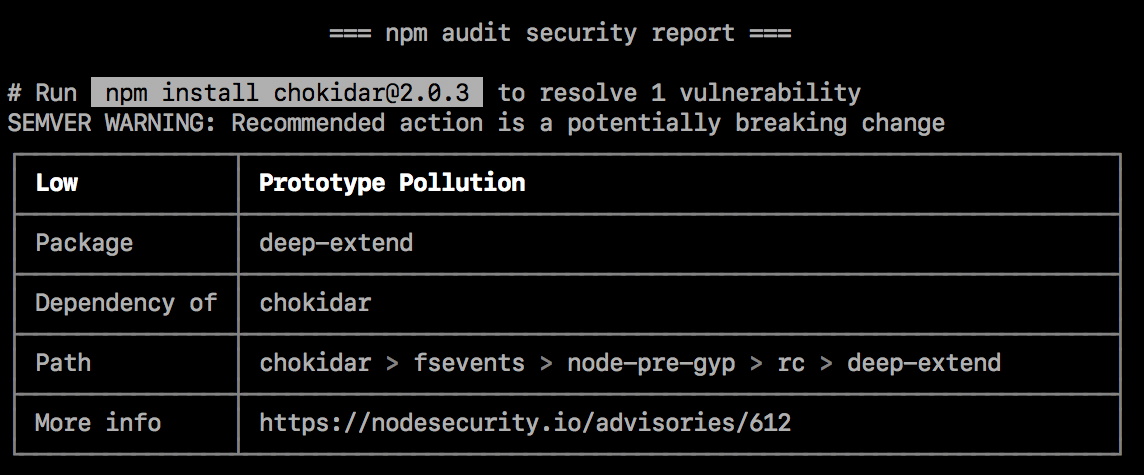
Auditing package dependencies for security vulnerabilities

What Is a Security Vulnerability? Definition, Types, and Best Practices for Prevention - Spiceworks
VDP Programs/Platform & Security
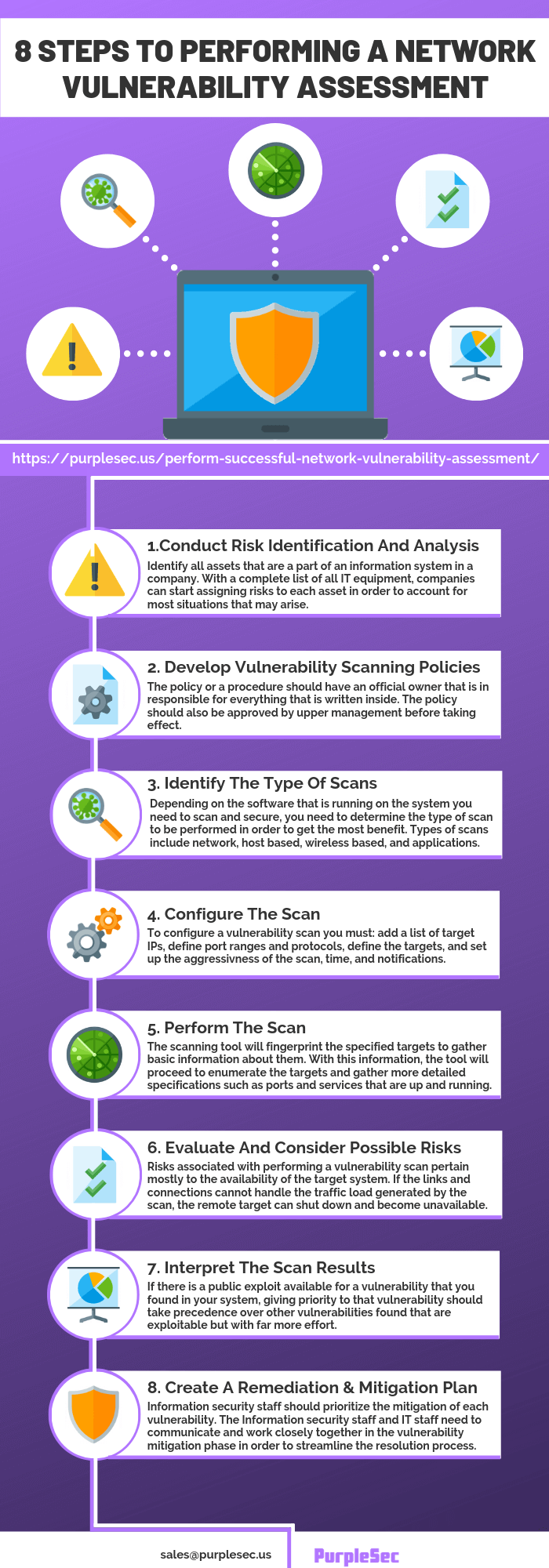
How To Conduct A Vulnerability Assessment In 8 Steps
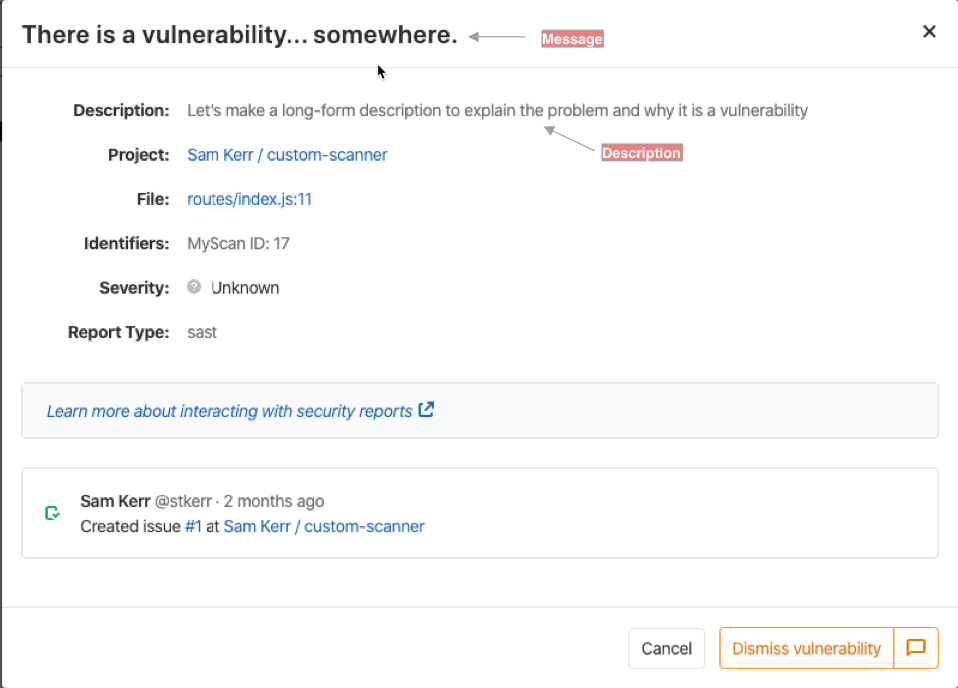
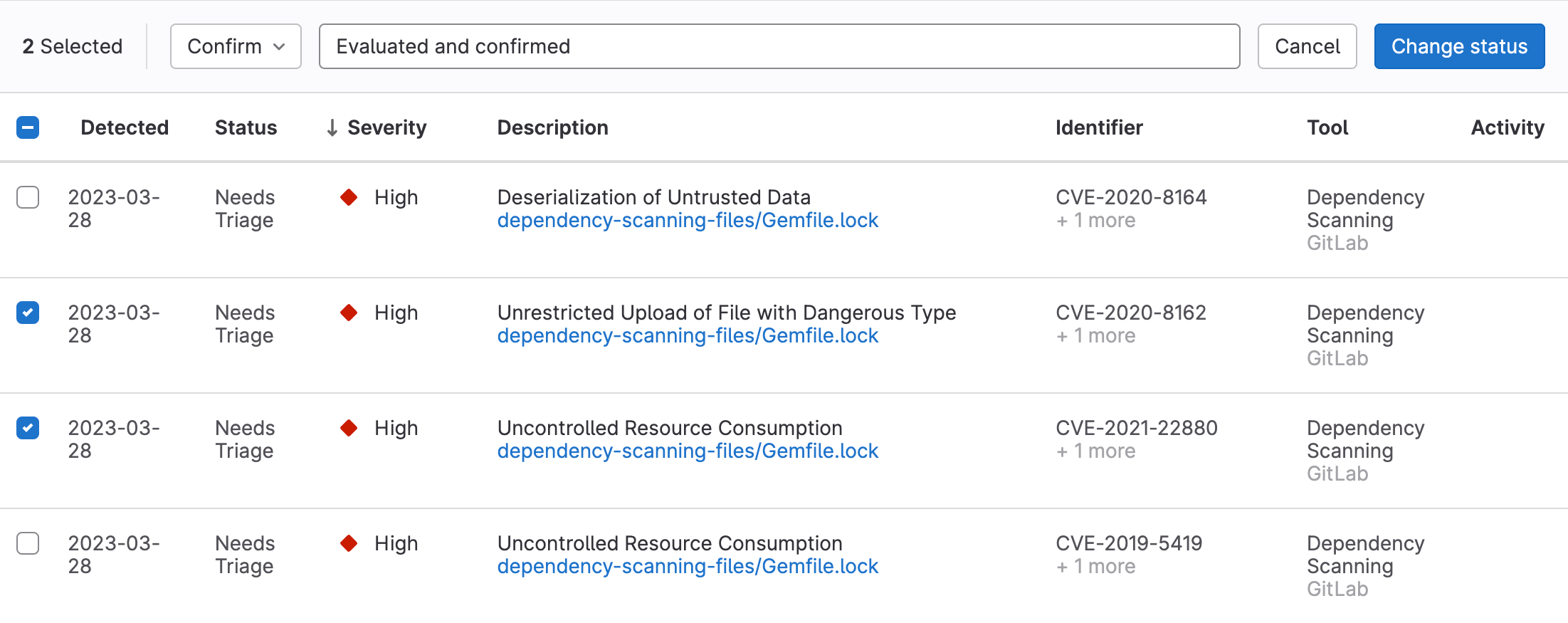
Security scanner integration
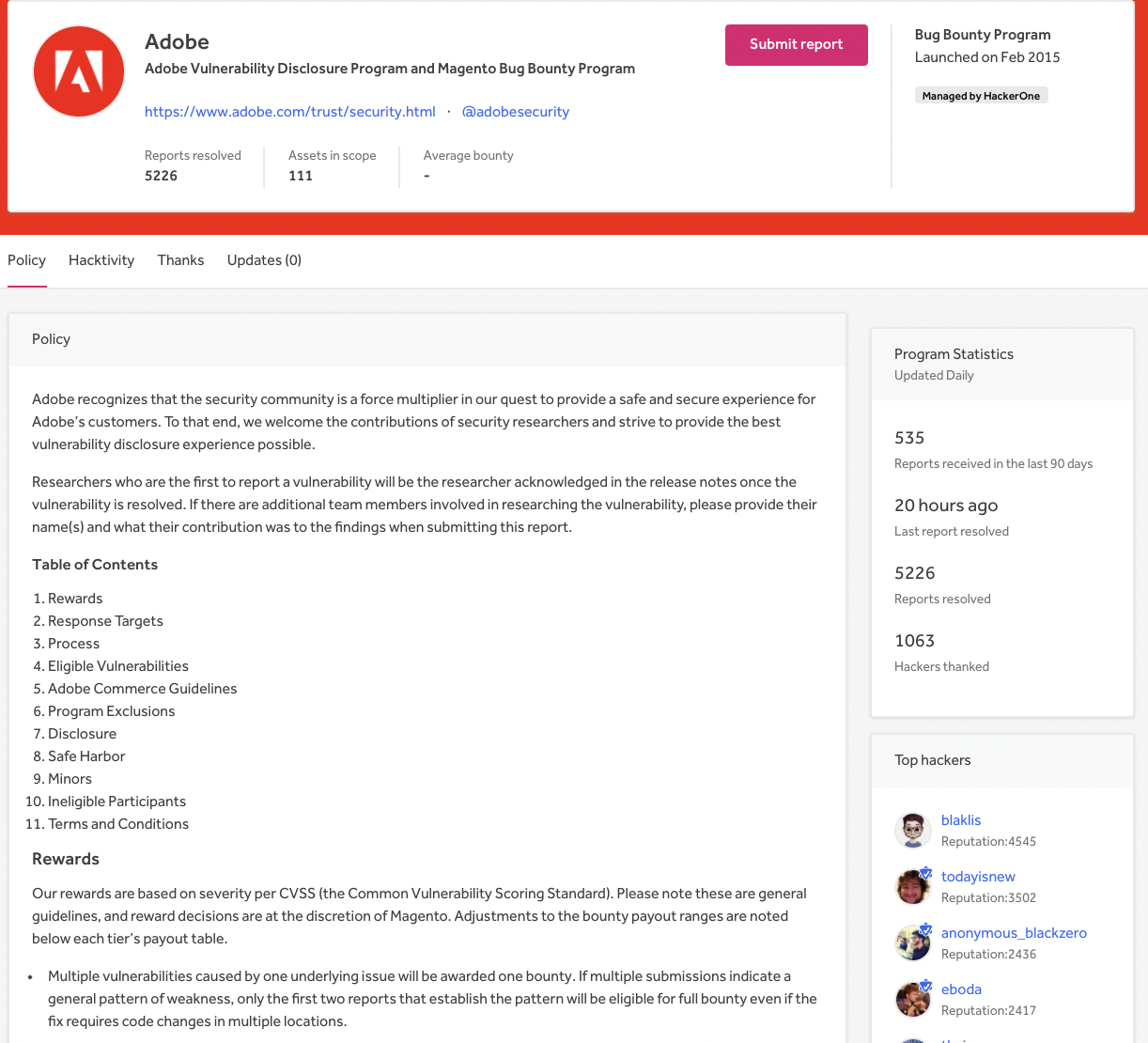
Bug Bounty vs. VDP, Which Program Is Right for You?
How To Conduct A Security Risk Assessment

What Is a Security Vulnerability? Definition, Types, and Best Practices for Prevention - Spiceworks